Tor : The Onion Router
Tor (The Onion Router) is a very sophisticated network of proxy servers.
When you use Tor to access a Web site, your communications are randomly routed through a network of independent, volunteer proxies. All the traffic between Tor servers (or relays) is encrypted, and each of the relays knows only the IP address of two other machines – the one immediately previous to it and the one immediately after it in the chain.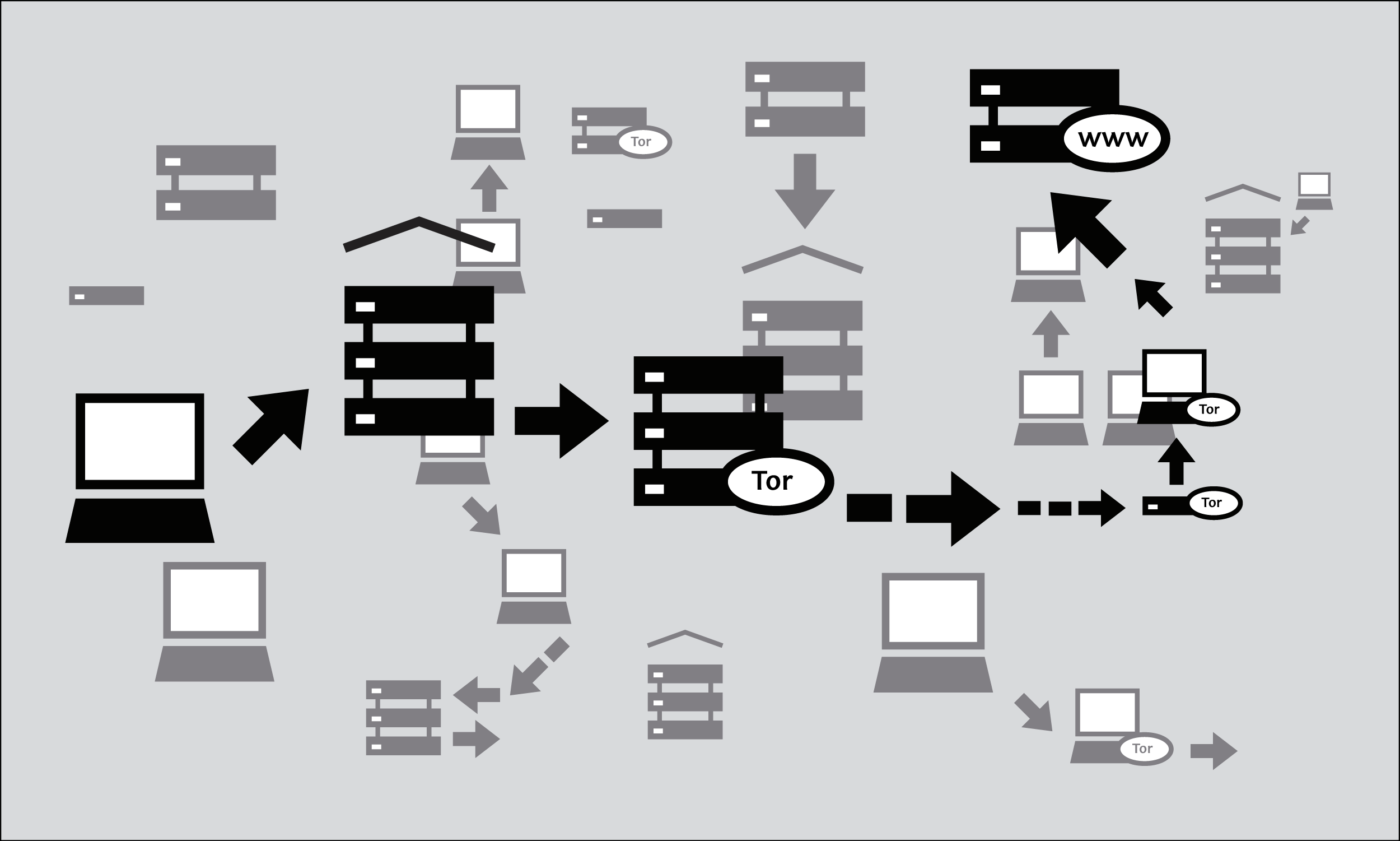
The goal of this is unlinkability. Tor makes it very difficult for:
- your ISP or any other local observer to know what your target Web site is or what information you are sending
- the target Web site to know who you are (at least, to know your IP address)
- any of the independent relays to know who you are and where you go either by directly having your IP address or by being able to correlate browsing habits by consistently observing your traffic.
What do I need to use the Tor network?
To connect to the Internet through the Tor network and use it for anonymity, privacy, and circumvention, you need to install the Tor client software on your computer. It is also possible to run a portable version of the program from a USB flash drive or other external device.
Tor is compatible with most versions of Windows, Mac OS X, and GNU/Linux.
With what software is Tor compatible?
Tor uses a SOCKS proxy interface to connect to applications, so any application that supports SOCKS (versions 4, 4a and 5) can have its traffic anonymized with Tor, including:
- most Web browsers
- many instant messaging and IRC clients
- SSH clients
- e-mail clients.
If you installed Tor from the Vidalia Bundle, Tor Browser Bundle or Tor IM Browser Bundle, Tor will have also configured an HTTP application proxy as a front-end to the Tor network. This will allow some applications that do not support SOCKS to work with Tor.
If you are mostly interested in using Tor for Web surfing and chatting, you may find it easiest to use the Tor Browser Bundle or the Tor IM Browser Bundle which will provide you with ready-to-use pre-configured solutions. The Tor Browser Bundle also includes Torbutton, which improves privacy protection when using Tor with a Web browser. Both versions of Tor can be downloaded at https://www.torproject.org/projects/torbrowser.
Advantages and Risks
Tor can be a very effective tool for circumvention and protecting your identity. Tor's encryption hides the contents of your communications from your local network operator, and conceals whom you are communicating with or what Web sites you're viewing. When used properly, it provides significantly stronger anonymity protection than a single proxy.
But:
- Tor is vulnerable to blocking. Most Tor nodes are listed in a public directory, so it is easy for network operators to access the list and add the IP addresses of nodes to a filter. (One way of attempting to get around this kind of blocking is to use one of several Tor bridges, which are Tor entry nodes not publicly listed, specifically to avoid blocking.)
- Some programs you might use with Tor have problems that can compromise anonymity. The Tor Browser Bundle comes with a version of Firefox with Torbutton installed. Torbutton disables some plugins and changes your browser fingerprint so it looks like any other Torbutton user. Tor will not protect you if you do not configure your appplications to run through Tor. Some plugins and scripts ignore local proxy settings and can reveal your IP address.
- If you're not using additional encryption to protect your communications, your data will be unencrypted once it reaches the last Tor node in the chain (called an exit node). This means that your data will be potentially visible to the owner of the last Tor node and to the ISP between that node and your destination Web site.
- Tor does not protect you if you do not use it correctly. Read the list of warnings here: https://www.torproject.org/download/download.html.en#warning and then make sure to follow the instructions for your platform carefully: https://www.torproject.org/documentation.html.en#RunningTor
- Even if you configure and use Tor correctly, there are still potential attacks that could compromise Tor's ability to protect you: https://trac.torproject.org/projects/tor/wiki/TheOnionRouter/TorFAQ#Whatattacksremainagainstonionrouting
- No anonymity system is perfect these days, and Tor is no exception: you should not rely solely on the current Tor network if you really need strong anonymity.
Using Tor Browser Bundle
The Tor Browser Bundle lets you use Tor on Windows, OS X, or GNU/Linux without requiring you to configure a Web browser. Even better, it's also a portable application that can be run from a USB flash drive, allowing you to carry it to any computer without installing it on each computer's hard drive.
Downloading Tor Browser Bundle
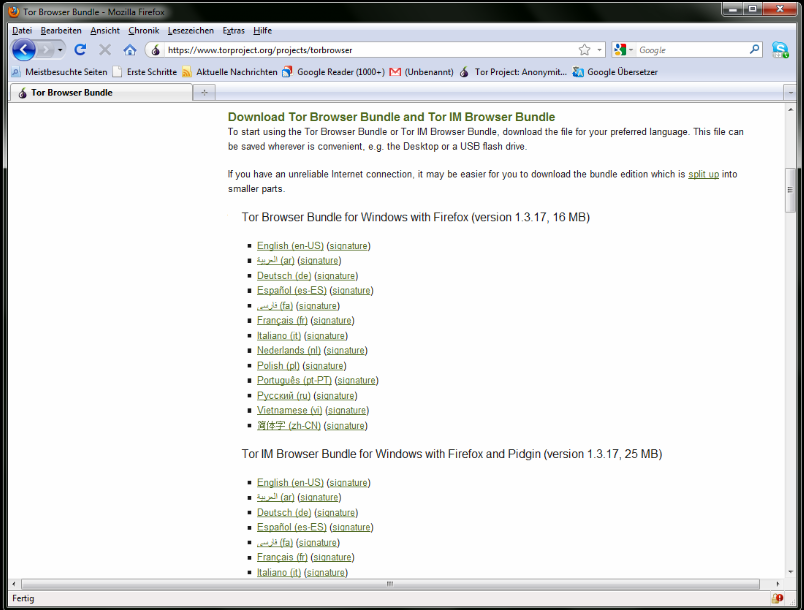
You can download the Tor Browser Bundle from the torproject.org Web site, either as a single file or a "split" version that is multiple files. If your Internet connection is slow and unreliable, the split version may work better than trying to download one very large file.
If the torproject.org Web site is filtered from where you are, type "tor mirrors" in your favorite Web search engine; the results will probably include some alternative addresses to download the Tor Browser Bundle.
Get Tor through e-mail: send an e-mail to gettor@torproject.org with "help" in the message body, and you will receive instructions on how to have the autoresponder bot send you the Tor software.
Caution: When you download the Tor Browser Bundle (plain or split versions), you should check the signatures of the files, especially if you are downloading the files from a mirror site. This step ensures that the files have not been tampered with. To learn more about signature files and how to check them, read https://www.torproject.org/docs/verifying-signatures.
You can download the GnuPG software that you will need to check the signature here: http://www.gnupg.org/download/index.en.html#auto-ref-2.
The instructions below refer to installing Tor Browser on Microsoft Windows. If you are using a different operating system, refer to the Tor Web site for download links and instructions.
Installing from a single file
- In your Web browser, enter the download URL for Tor Browser: https://www.torproject.org/projects/torbrowser
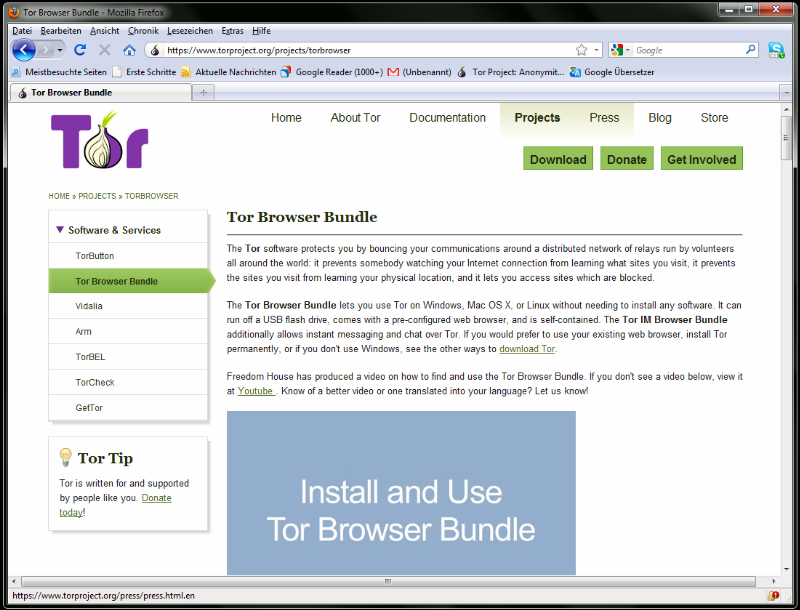
- Click the link for your language to download the installation file.
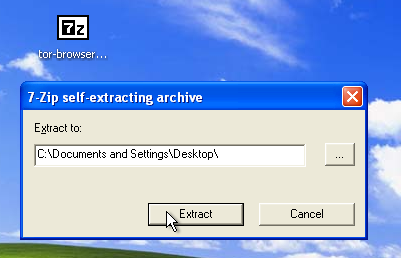
- Double-click the .exe file that you have now downloaded. A "7-Zip self-extracting archive" window appears.
- Choose a folder into which you want to extract the files and click Extract.
Note: you can choose to extract the files directly onto a USB flash drive if you want to use Tor Browser on different computers (for instance on public computers in Internet cafés). -
When the extraction is completed, open the folder and check that the contents match the image below:

To clean up, delete the .exe file you originally downloaded.
Installing from split files
- In your Web browser, enter the URL for the split version of the Tor Browser Bundle (https://www.torproject.org/projects/torbrowser-split.html.en), then click the link for your language to get to a page that looks like the one for English below:
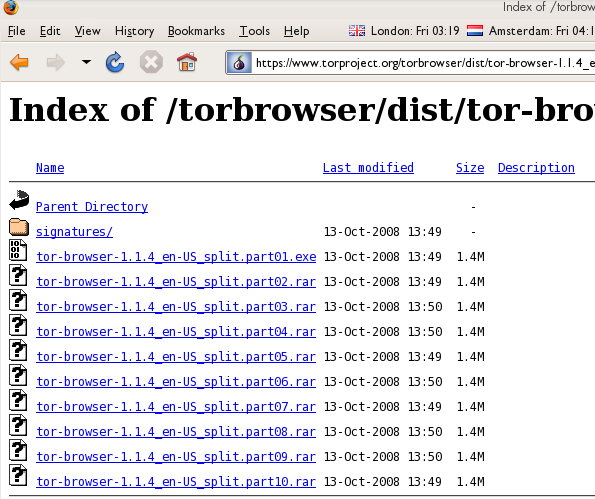
- Click each file to download it (one ending in .exe and nine others ending in .rar), one after the other, and save them all in one folder on your hard drive.
- Double-click the first part (the file whose name ends in .exe). This runs a program to gather all the parts together.
"Split installer for Tor Browser Bundle" src="_booki/summary-of-firefox/static/CircumventionTools-InstallingTor-tor_winrar_2-en.png" height="384" width="562">
- Choose a folder where you want to install the files, and click Install. The program displays progress messages while it's running, and then quits.
- When the extraction is completed, open the folder and check that the contents match the image below:

- To clean up, delete all the files you originally downloaded.
Using Tor Browser
Before you start:
- Close Tor. If Tor is already installed on your computer, make sure it is not currently running.
Launch the Tor Browser:
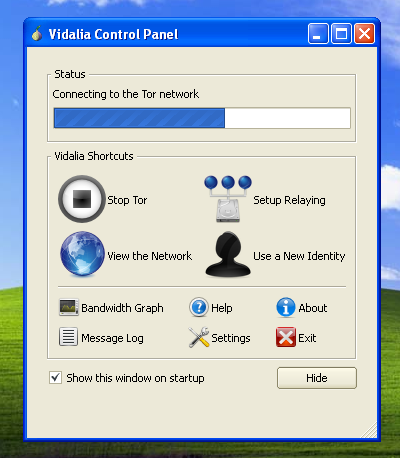
In the Tor Browser folder, double-click Start Tor Browser. The Tor control panel (Vidalia) opens and Tor starts to connect to the Tor network.
When a connection is established, Firefox automatically connects to the TorCheck page and then confirms that your browser is configured to use Tor. This may take some time, depending on the quality of your Internet connection.
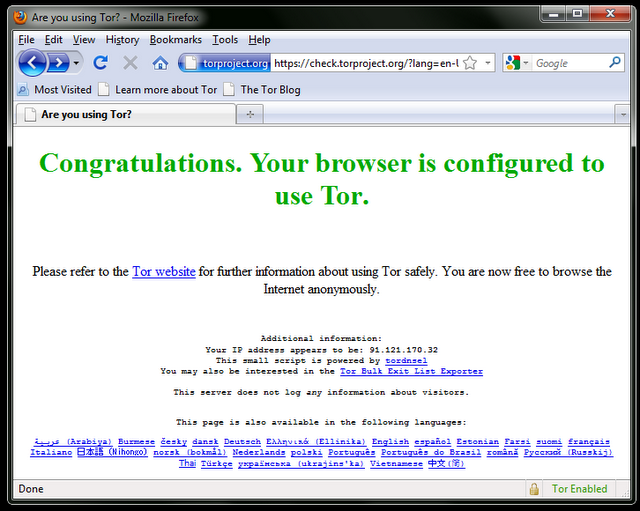
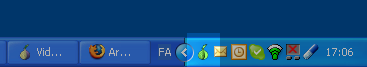
If you are connected to the Tor network, a green onion icon appears in the system tray on the lower-right-hand corner of your screen:
Browsing the Web using Tor Browser
Try viewing a few Web sites, and see if they are working. The sites are likely to load more slowly than usual because your connection is being routed through several relays.
If this does not work
If the onion in the Vidalia Control Panel never turns green or if Firefox opened, but displayed a page saying "Sorry. You are not using Tor", as in the image below, then you are not using Tor.
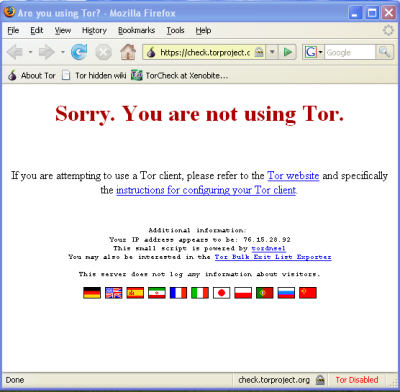
If you see this message, close Firefox and Tor Browser and then repeat the steps above. You can perform this check to ensure that you are using Tor at any time by going to https://check.torproject.org/.
If Tor Browser doesn't work after two or three tries, Tor may be partly blocked by your ISP and you should try using the bridge feature of Tor – see the section below on "Using Tor with Bridges".
Using Tor with Bridges
If you suspect your access to the Tor network is being blocked, you may want to use the bridge feature of Tor. The bridge feature was created specifically to help people use Tor from places where access to the Tor network is blocked. You must already have successfully downloaded and installed the Tor software to use a bridge.
What is a bridge?
Bridge relays (or bridges for short) are Tor relays that aren't listed in the main public Tor directory. This is a deliberate measure to stop these relays from being blocked. Even if your ISP is filtering connections to all the publicly known Tor relays, it may not be able to block all the bridges.
Where do I find bridges?
To use a bridge, you need to locate one and add its information in your network settings. A simple way to get a few bridges is by simply accessing https://bridges.torproject.org/ with your Web browser. If that Web site is blocked or you need more bridges, send an e-mail from a Gmail account to bridges@torproject.org with "get bridges" (without the quotemarks) in the body of the message.
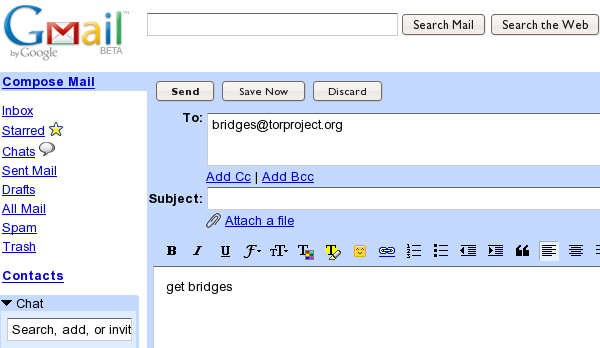
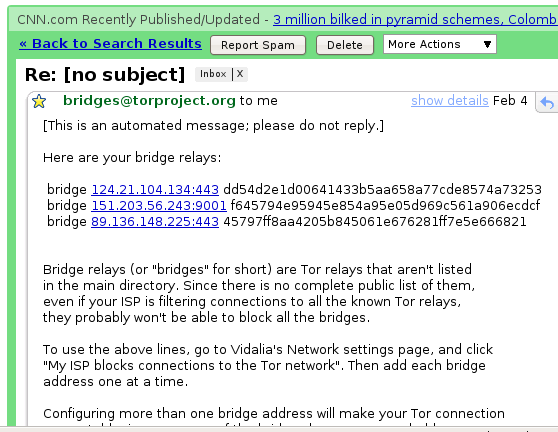
Almost instantly, you will receive a reply that includes information about a few bridges:
Important Notes:
- You must use a Gmail account to send the request. If torproject.org accepted requests from other mail accounts, an attacker could easily create a lot of email addresses and quickly learn about all the bridges. If you do not have a Gmail account already, creating one takes only a few minutes.
- If you are on a slow Internet connection you can use the URL https://mail.google.com/mail/h/ for a direct access to the basic HTML version of Gmail.
Turn on bridging and enter bridge information
After you get addresses for some bridge relays, you must configure Tor with whatever bridge address you intend to use:
- Open the Tor control panel (Vidalia).
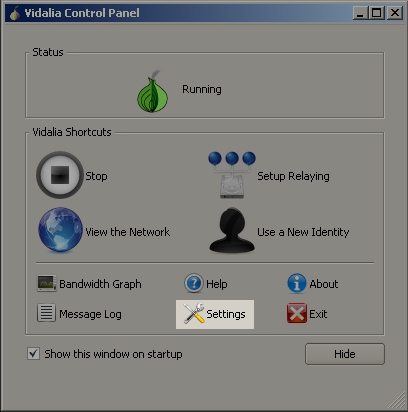
-
Click Settings. A Settings window opens.
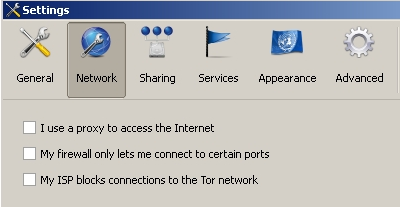
- Click Network.
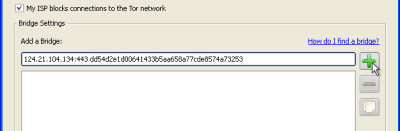
- Select "My Firewall only lets me connect to certain ports" and "My ISP blocks connections to the Tor network".
- Enter the bridge URL information you received by e-mail in the "Add a Bridge" field.
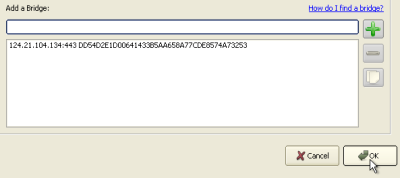
- Click the green + on the right side of the "Add a Bridge" field. The URL is added to the box below.
- Click OK at the bottom of the window to validate your new settings.
- In the Tor control panel, stop and restart Tor to use your new settings.
Note:
Add as many bridge addresses as you can. Additional bridges increase reliability. One bridge is enough to reach the Tor network, however if you have only one bridge and it gets blocked or stops operating, you will be cut off from the Tor network until you add new bridges.
To add more bridges in your network settings, repeat the steps above with the information on the additional bridges that you got from the bridges@torproject.org e-mail message.