Introduction to e-mail safety
 E-mail is one of the oldest forms of communication on the Internet. We often use it to communicate very personal or otherwise sensitive information. It is very important to understand why e-mail in its default configuration is not secure. In the following chapters we will describe the different methods necessary to secure your e-mail against known threats. We will also provide you with basic knowledge to assess the risks involved in sending and receiving e-mail. This section will start by describing the security considerations when using e-mail.
E-mail is one of the oldest forms of communication on the Internet. We often use it to communicate very personal or otherwise sensitive information. It is very important to understand why e-mail in its default configuration is not secure. In the following chapters we will describe the different methods necessary to secure your e-mail against known threats. We will also provide you with basic knowledge to assess the risks involved in sending and receiving e-mail. This section will start by describing the security considerations when using e-mail.
No sender verification: you cannot trust the 'from' address
 Most people do not realize how trivial it is for any person on the Internet to forge an e-mail by simply changing the identity profile of their own e-mail program. This makes it possibly for anyone to send you an e-mail from some known e-mail address, pretending to be someone else. This can be compared with normal mail; you can write anything on the envelope as the return address, and it will still get delivered to the recipient (given that the destination address is correct). We will describe a method for signing e-mail messages, which prevents the possibility of forgery. Signing e-mail messages will be explained in the chapter about PGP (Pretty Good Privacy).
Most people do not realize how trivial it is for any person on the Internet to forge an e-mail by simply changing the identity profile of their own e-mail program. This makes it possibly for anyone to send you an e-mail from some known e-mail address, pretending to be someone else. This can be compared with normal mail; you can write anything on the envelope as the return address, and it will still get delivered to the recipient (given that the destination address is correct). We will describe a method for signing e-mail messages, which prevents the possibility of forgery. Signing e-mail messages will be explained in the chapter about PGP (Pretty Good Privacy).
E-mail communications can be tapped, just like telephones
An e-mail message travels across many Internet servers before it reaches its final recipient. Every one of these servers can look into the content of messages, including subject, text and attachments. Even if these servers are run by trusted infrastructure providers, they may have been compromised by hackers or by a rogue employee, or a government agency may seize equipment and retrieve your personal communication.
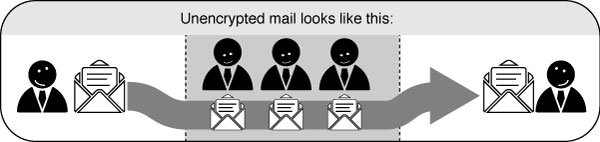
There are two levels of security that protect against such e-mail interception. The first one is making sure the connection to your e-mail server is secured by an encryption mechanism. The second is by encrypting the message itself, to prevent anyone other than the recipient from understanding the content. Connection security is covered extensively in this section and in the sections about VPN. E-mail encryption is also covered in detail in the chapters about using PGP.
Mail hoaxes, viruses and spam
 More than 80% of all the traffic coming through a typical e-mail server on the Internet contains either spam messages, viruses or attachments that intend to harm your computer. Protection against such hostile e-mails requires keeping your software up-to-date and having an attitude of distrust toward any e-mail that cannot be properly authenticated. In the final chapter of this section, we will describe some ways to protect against hostile e-mail.
More than 80% of all the traffic coming through a typical e-mail server on the Internet contains either spam messages, viruses or attachments that intend to harm your computer. Protection against such hostile e-mails requires keeping your software up-to-date and having an attitude of distrust toward any e-mail that cannot be properly authenticated. In the final chapter of this section, we will describe some ways to protect against hostile e-mail.
Fraudulent mails requesting 'personal information'
Your internet service provider, your phone company, your bank or any reputable institution will never ask you to supply them with your username or password. They will also never send you an email or even telephone you and ask for confidential information regarding your account or setup. They will never require you to visit some website in order to 'fix' something with your computer. Whenever you receive such a request, you can be certain that it is a malicious attempt by a third-party to steal your account information. Such attempts are called 'Phishing attacks' in internet jargon, and are very common. Remember, reputable companies are hosting your data and should not require any such information from you.
Unverified mails from organizations or individuals offering you a 'service'
Phishing attacks can come from a wide variety of sources. You may receive mails from an organization or an individual who offers to assist you with some problem or provide you with some service. For example, you might receive an e-mail that looks like it is from the company who makes the anti-virus program you to use. The message says that there is an important update to their software. They have conveniently attached a handy executable file that will automatically fix your software.
Because the sender of the message cannot be verified, such messages should be immediately discarded, as the attached file almost certainly contains a virus or hostile program.
Mails with attachments
You may receive a message from a friend that contains an attachment. In the message, your friend might say that the attachment is a great game, or a handy utility, or anything else. Computer systems infected with viruses can "hijack" email accounts and send these kinds of messages to everyone in a person's address book. The message is not from your friend - it is from a virus that has infected your friend's computer system.
 Only open attachments when you have verified the sender's address. This applies to attachments of any type, not just executable files. Viruses can be contained in almost any type of file: videos, images, audio, office documents. Running an anti-virus program or a spam filter provides some protection against these hostile mails, as they will warn you whenever you download an infected file or a trojan. However, you should not count entirely on your anti-virus programs or spam filters, because they are only effective against threats that they know about. They cannot protect you from threats that have not yet been included in their definition files. (That is why it is important to keep your anti-virus and anti-spam definition files up to date.)
Only open attachments when you have verified the sender's address. This applies to attachments of any type, not just executable files. Viruses can be contained in almost any type of file: videos, images, audio, office documents. Running an anti-virus program or a spam filter provides some protection against these hostile mails, as they will warn you whenever you download an infected file or a trojan. However, you should not count entirely on your anti-virus programs or spam filters, because they are only effective against threats that they know about. They cannot protect you from threats that have not yet been included in their definition files. (That is why it is important to keep your anti-virus and anti-spam definition files up to date.)
The safest approach regarding email attachments is to never open an attachment unless you are completely certain that it originates from a known, trusted source.
Compromise by malware
Even if you have verified all your email and have only opened those attachments that you have deemed safe, your computer may still be infected by a virus. For example, your friend may have inadvertently sent you a document that contains a virus. Malware detection can be difficult, although it is usually detected by anti-virus programs (assuming that the definition files are current, as described above). Signs of active malware can include:
- a sudden slowdown of your computer or internet connection
- strange pop-up messages appearing while using your computer
- complaints from your internet service provider regarding abuse of your account (for example, claiming that you have been sending spam messages)





